Technology modernisation has become a constant drumbeat across the public sector - and for good reason. The opportunities offered by modern, integrated systems are clear: better data access, streamlined processes, and more responsive public services.
Modernising policing without disruption
By Ian Whitehead, Ex Senior Officer and Strategic Advisor for Security & Justice on Oct 15, 2025
Agentforce - security breach explained
By Santosh Sundar on Oct 3, 2025
I’m sure we are all aware that AI is advancing at an unprecedented rate. With every breakthrough comes both a new set of opportunities and a group of risks. While the potential of AI is huge, the reality is clear: without security and compliance at its core, innovation can quickly turn into exposure.
A recent discovery of a vulnerability in Salesforce's Agentforce is a timely reminder that even the most established platforms aren't invincible. And whilst Salesforce quickly resolved the issue, it raises important questions about how we manage AI responsibly, protect sensitive data, and keep trust at the heart of every solution.
Summer 2025 Anypoint Code Builder Release
By Olga Kepa, MuleSoft Developer on Sep 15, 2025
Now that summer is coming to an end here in the UK, it’s time to look back at some more exciting features introduced by MuleSoft over the last few months. So in saying that, welcome to the 9th blog in the series on Anypoint Code Builder!
Why it’s time to embrace disruptive technology in policing
By Ian Whitehead, Ex Senior Officer and Strategic Advisor for Security & Justice on Aug 12, 2025
After three decades in policing, including 15 years in senior leadership, I’ve seen first-hand the impact that legacy technology has on frontline delivery. It’s not just about systems that feel outdated or unintuitive. It’s about the deep-rooted inefficiencies and limitations that hold back people who are doing critical public service work.
Building with Agentforce in MuleSoft Anypoint Code Builder
By Olga Kepa, MuleSoft Developer on Jun 2, 2025
It’s been a while since my last write up on MuleSoft Anypoint Code Builder. While several new features have been introduced this year, I want to focus on MuleSoft’s artificial intelligence (AI) integrations. Let’s be honest, AI has been a hot topic for a while and isn’t going away anytime soon. So in this blog, I’ll guide you through using the Agentforce Generative Flow feature in Anypoint Code Builder and also share some practical tips along the way to help you get the most out of it.
October 2024 Anypoint Code Builder Release
By Olga Kepa, MuleSoft Developer on Dec 2, 2024
Have you checked out Anypoint Code Builder lately? There has been another major release since my last blog, but don't worry, I’m here to guide you through the recent changes.
Using AWS service role in CloudHub 2.0
By Guilherme Pereira, Senior Integration Consultant on Oct 28, 2024
AWS Service Roles allow services to securely interact with other AWS services on your behalf by assuming roles with the necessary permissions. This simplifies access management and reduces the need to handle long-term credentials.
CloudHub 2.0 works on top of an AWS EKS service, so we can leverage AWS Service Roles to connect our APIs with many other AWS services used by our integrations, such as SQS, S3, DynamoDB, Secret Manager, etc.
In this article, we will see how it works and how to implement it.
Data 360 in higher education - more than just a system of record
By Alessandro Toscano, Solution Architect on Oct 14, 2024
In higher education, managing student data is often seen as a challenge of consolidating records across various platforms - from admissions and financial aid systems to student management portals and alumni databases. For many institutions, the complexity of these systems leads to fragmented data, making it hard to get a unified view of students and make timely, data-driven decisions.
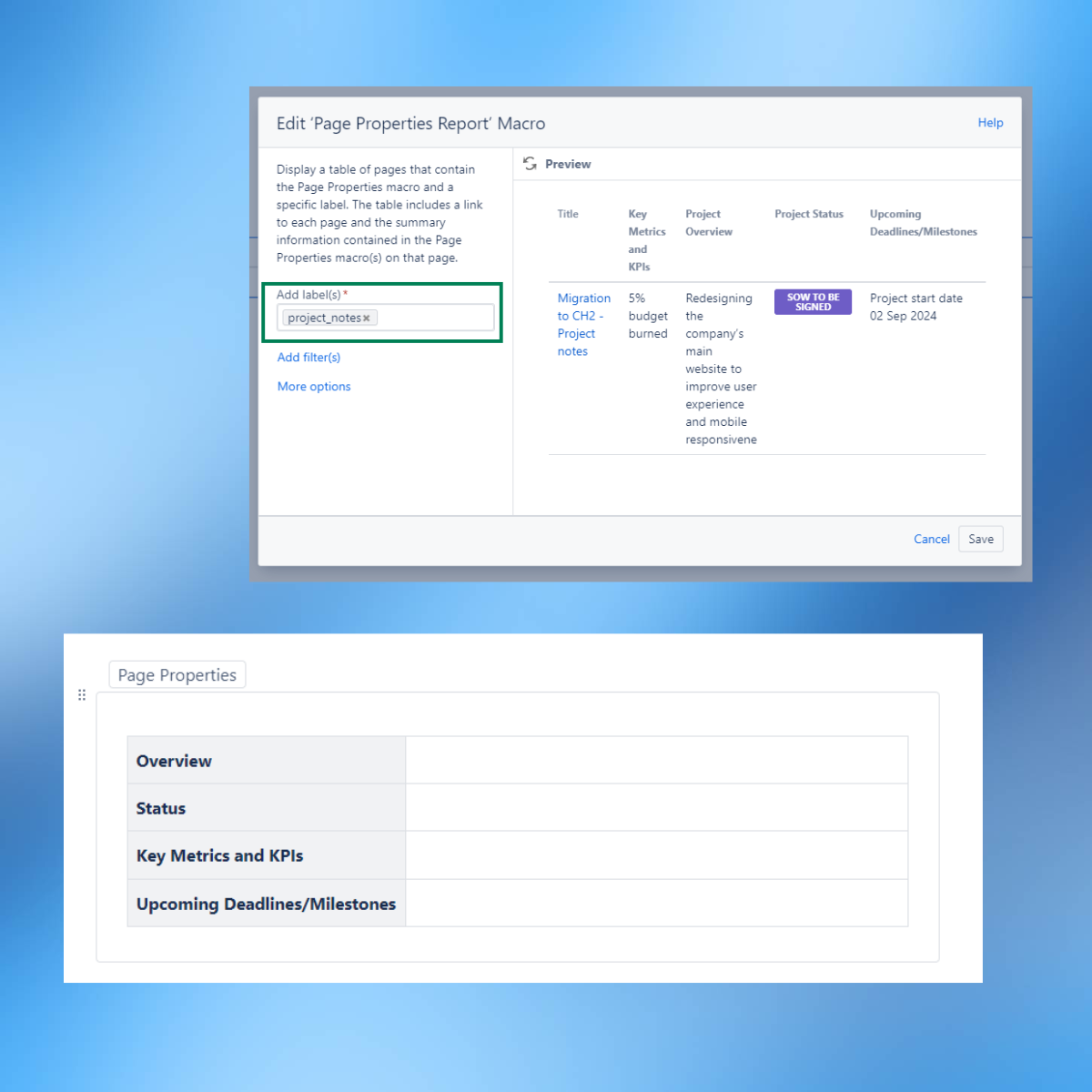
How to set up Confluence to manage multiple projects
By Giulia Fabiano, Project Manager on Sep 19, 2024
As a project manager, I often have multiple projects running parallel to one another. Before building a solid approach to monitor all these tasks and activities in progress, I always worried I might miss something.
Setting Boundaries in Hyperautomation Projects
By Siddharth Sharma on Aug 14, 2024
Working in the automation space is both exciting and challenging. In a recent hyperautomation project with a client, I was provided invaluable insights into the complexities and nuances of automating business processes using MuleSoft RPA.
Here's a detailed look at my experience, the challenges faced and the lessons learned, along with a project glance on automating quotes in Excel and PDF formats.



.png)

.png)
.png)

.png)

