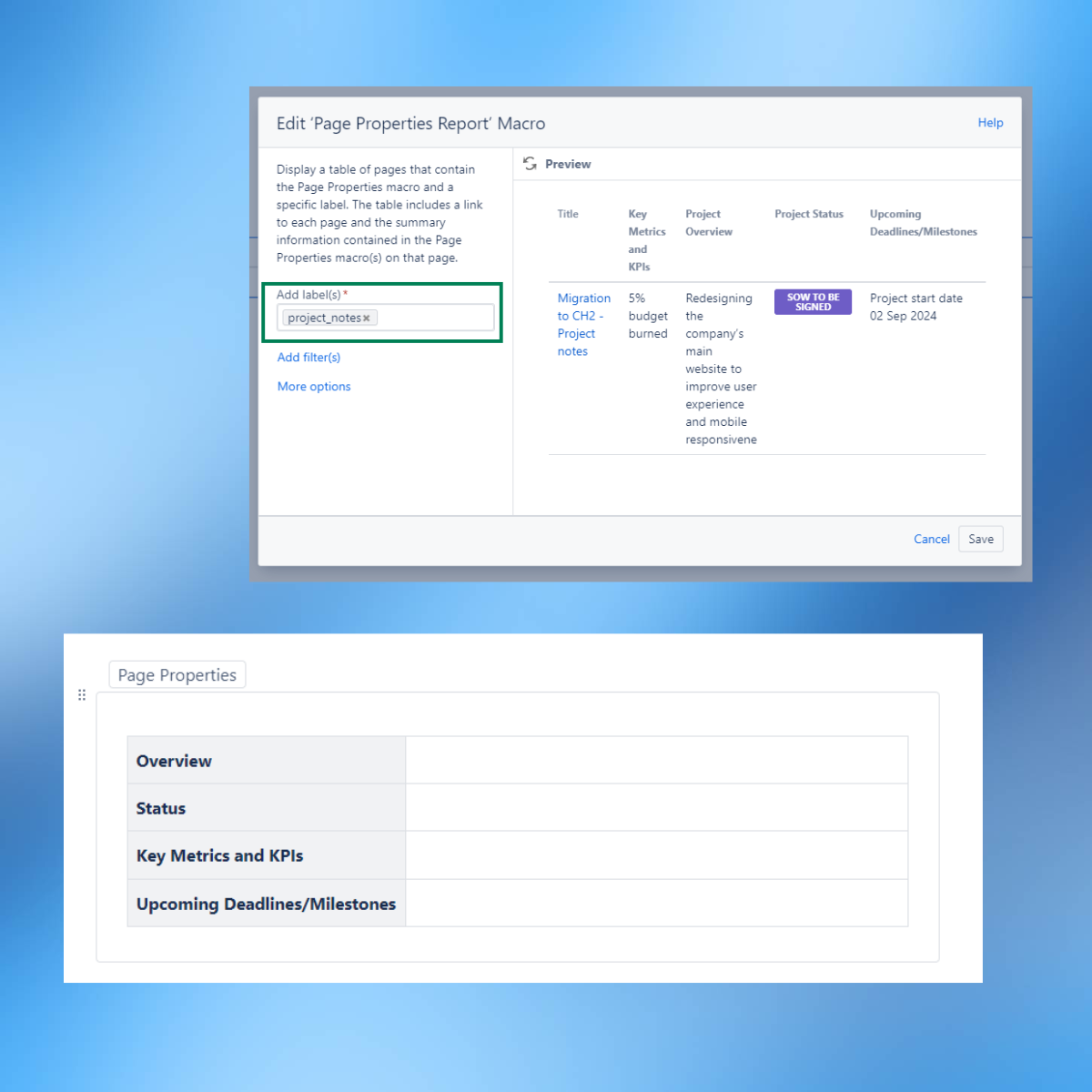
As a project manager, I often have multiple projects running parallel to one another. Before building a solid approach to monitor all these tasks and activities in progress, I always worried I might miss something.
How to set up Confluence to manage multiple projects
By Giulia Fabiano, Project Manager on Sep 19, 2024
Spring Cleaning your Marketing Data
By Samantha Schwab on Feb 15, 2024
In the fast-paced world of marketing, many people don’t realise what the true foundation is of a successful campaign strategy. While flashy creatives and catchy taglines draw attention, there is a much more essential key to conversion: clean data.
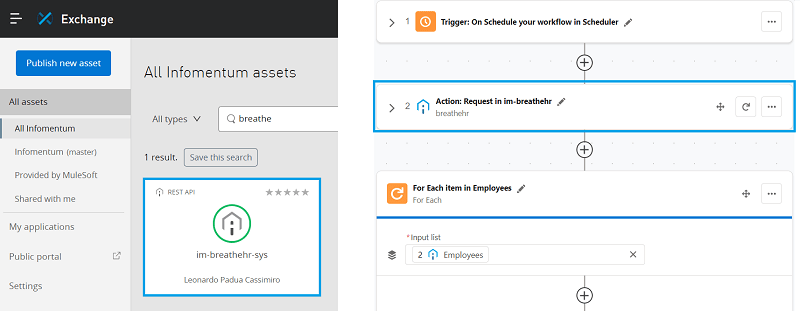
MuleSoft Anypoint Platform: API Sharing for Composer and RPA
By Leonardo Cassimiro on Mar 10, 2023
MuleSoft Composer is a no-code integration platform that enables users to integrate data and apps easily. The process starts by building flows using various pre-built connectors, including Salesforce, Workday, Slack, MuleSoft RPA, and others.
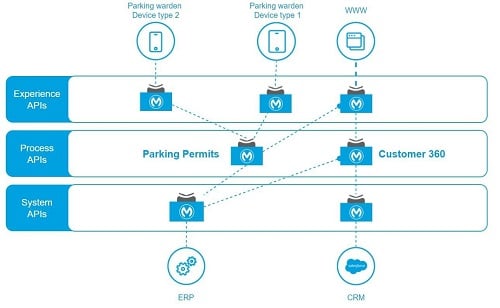
The real value of API-led connectivity from a Project Manager perspective
By Giulia Fabiano, Project Manager on Aug 31, 2022
I often felt a step behind my team at the start of new projects implementing system integration. Such projects are very technical and could be overwhelming for a Project Manager like me. I was drowning in tech details and scary-sounding abbreviations.
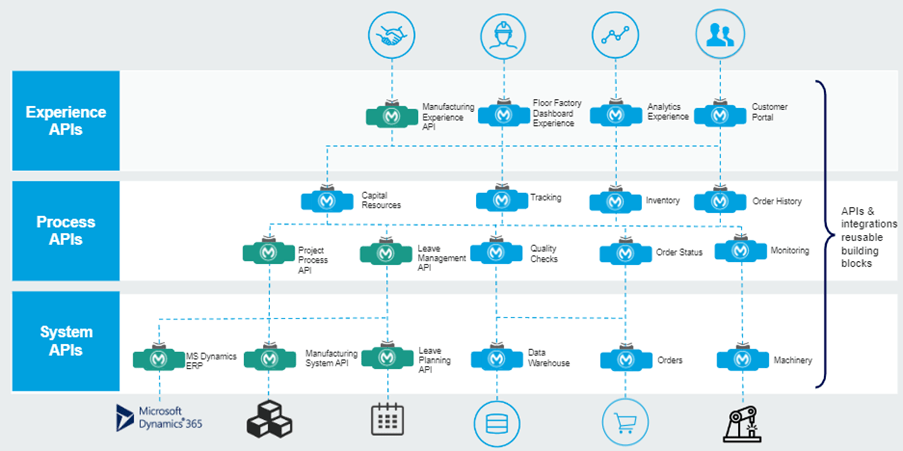
Manufacturing with MuleSoft, creating exponential value
By Anthony de Wouters on Aug 3, 2022
Navigating the world of manufacturing can be a complex and exciting experience. Whilst this could be said for most companies and industries, this proved more so the case when Infomentum recently delivered a proof of concept. This organisation not only finds itself at the heart of UK-based manufacturing but also at a junction between academia and government research. A solution was required to bridge the gap from both a technological and operational perspective.
When no one is perfect: how to provide negative feedback
By Shaha Alam on Jun 28, 2022
I've recently had the opportunity to reflect upon our annual staff appraisal process, specifically around the quality of feedback. One frequent observation is that reviews and comments often lack details, making appraisals challenging. It is especially true for managers who don't work closely with the appraisee and rely entirely on their colleagues' feedback to assess their progress. To address this issue, my colleague and I were asked to revisit the process and suggest what could be improved.
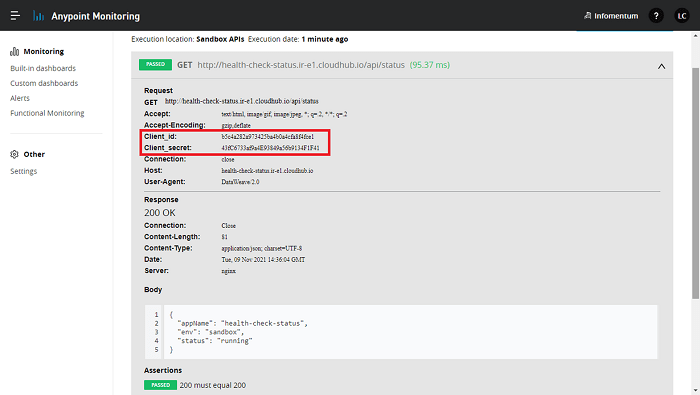
How to health check APIs using Anypoint Functional Monitoring with Secrets Manager
By Leonardo Cassimiro on Feb 16, 2022
When the connected digital experience has become "a must" rather than "a nice to be", integration solutions are in high demand. APIs are now almost the de factor way for various platforms and systems to communicate and exchange information. So, what happens when a public API fails? In 2014 Gartner estimated it to be about $300,000 per hour!
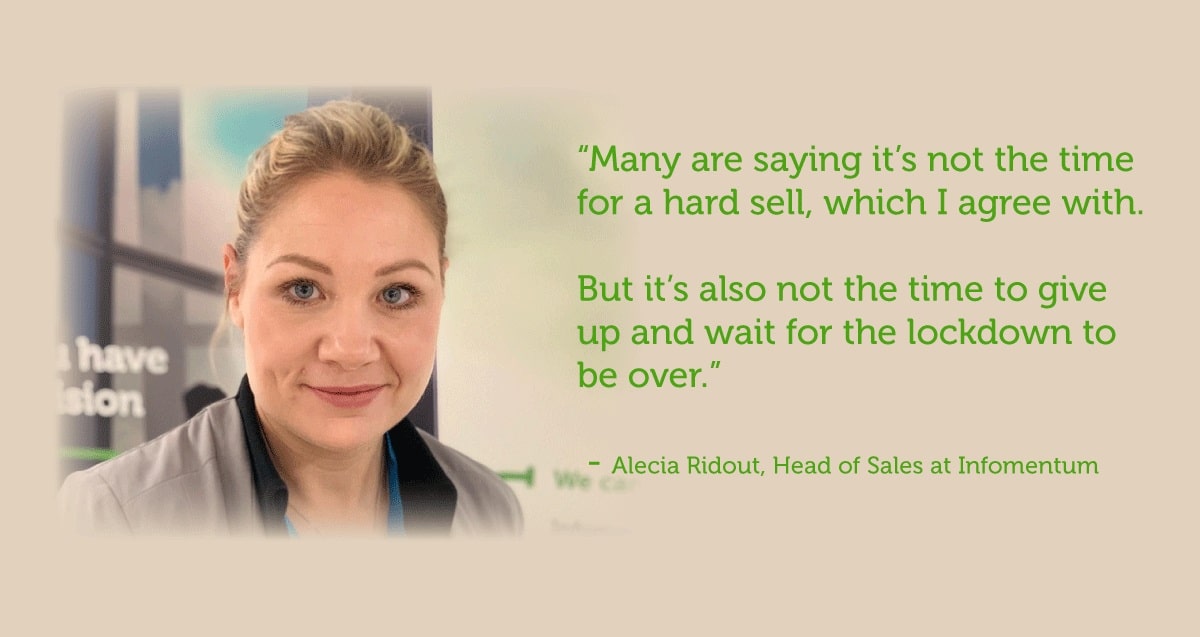
How to acquire new customers - drive B2B sales during the COVID-19
By Alecia Ridout, Head of Sales on Jun 26, 2020
The last few months have been challenging for most Sales teams, and ours has been no exception. The uncertainty of the economic climate has led many businesses to hibernate. In the space of a couple of weeks, the market went quiet; projects were put on hold, budgets cut.
Can you have engaging and effective Sprint Planning remotely?
By Andrew Murphy on May 5, 2020
According to the 6th principle of the Agile Manifesto: "The most efficient and effective method of conveying information to and within a development team is face-to-face conversation." So, does it mean that managing agile projects in the new world of large-scale remote working is impossible? Our answer is no! In the previous blog, we talked about how we ensure efficient communication with the home-based teams. In this blog, we discuss the important adjustments we’ve made to our remote Sprint Planning meetings as part of our Agile project delivery.
Key to remote project management success: get communications right
By Andrew Murphy on Apr 21, 2020
The quality of communication within a project team is often the most important aspect in the successful delivery of any project. Since our switch to remote working at the start of the pandemic, we’ve been faced with the challenge of using our project management tools in different ways to ensure that the quality of our communication and collaboration doesn’t suffer.